Hello, my name is Ryan and I am Chris’ friend. I trusted SMS-based 2FA because it sounded like a good idea (even though I read Cody Brown’s tale of woe, and Justin Williams just had almost the same experience I did).
So, here is a story about how calling T-Mobile to inquire about plan upgrades resulted in all of the money in my shared checking accounts getting wiped out – because SMS based 2FA is bad. Lessons learned are first, because maybe you don’t have time to read this whole thing.
This all went down in mid-July of this year.
What we learned
The post SMS 2FA is Better Than Nothing (here on this very blog!) is not…wrong. But it’s not right. SMS 2FA is only as strong as the mobile provider you have, and holy hell CSRs in a call center are probably not paid enough to think or care about this stuff. In Justin Williams’ case, the CSR wanted to make the customer happy (even if that meant breaking protocol). In my case, it meant…I don’t really know what it meant.
So:
- If you have SMS 2FA on important services (e.g., banking), if you get some weird text from your mobile provider about your SIM, call your bank ASAP and shout “FRAUD FRAUD FRAUD” until you get someone who can lock your account down.
- SMS 2FA is garbage. Don’t use it if you don’t have to.
- I am using an authenticator app. In my case, Symantec VIP (because my bank supports it and you can add QR Code 2FA from other services, like Google and Dropbox). My wife is getting a token from our bank.
- Unless T-Mobile comes out with some fantastic customer service to make up for all this fuckery, we’re switching providers (a bank representative has said they have seen this scenario before, mostly with T-Mobile).
Short Version
Feel free to read the timeline if you’d like. I am a bad editor, so it’s all there.
But from what we can piece together – based on what various customer service reps have said, and the timeline – it appears that a T-Mobile customer service rep had access to our account, as CSRs are supposed to have. Our account information showed the bank we use to pay our bill.
CSR decided to get into some 21st century theft (either by acting by his/herself or by providing this service to someone else). From here, we will refer to the “attacker”.
My wife’s number was ported to the attacker’s phone/device. The attacker assumed that my wife’s banking logon was the same as her email. In the 20 minutes (see Sunday – 7:20 pm) that my wife’s phone number was associated with another device, the attacker requested a password reset using SMS 2FA. Token was texted to attacker, and attacker was in the account.
From there, attacker reset all security (password, PIN, security questions) and linked checking accounts to a mobile wallet (activity that was verified by our bank) on an Android device. Mobile wallet was used to purchase the entire value of our checking accounts in Western Union money orders in Michigan (note – we do not live in Michigan).
Activity that should have caused a red flag but didn’t
- All security changed, and checking accounts linked to a mobile wallet on a new device.
- Spending of shit loads of money in a geographic region my wife has never been to.
Timeline
Please note that times are rough as this happened on a rather enjoyable family Sunday and I was not time stamping every activity like my bank account depended on it.
Sunday – 9 a.m.
My wife is tired of months of her iPhone 5s randomly dying when it has 75% battery life, so we poke around looking for prices on iPhone SEs (iPhones SE?). Turns out our carrier (T-Mobile) has some good pricing. So, she calls, and after speaking to a CSR (and giving the last 4 of her SSN (this is called foreshadowing) to verify her presence in the account), it turns out the pricing is only good if we up our data plan, which is not what we want to do, and she is frustrated so she hangs up.
Sunday – rest of the day
We walk around town with our daughter and generally hang out.
Sunday – 7:20 pm
My wife quickly gets two texts, one right after the other.
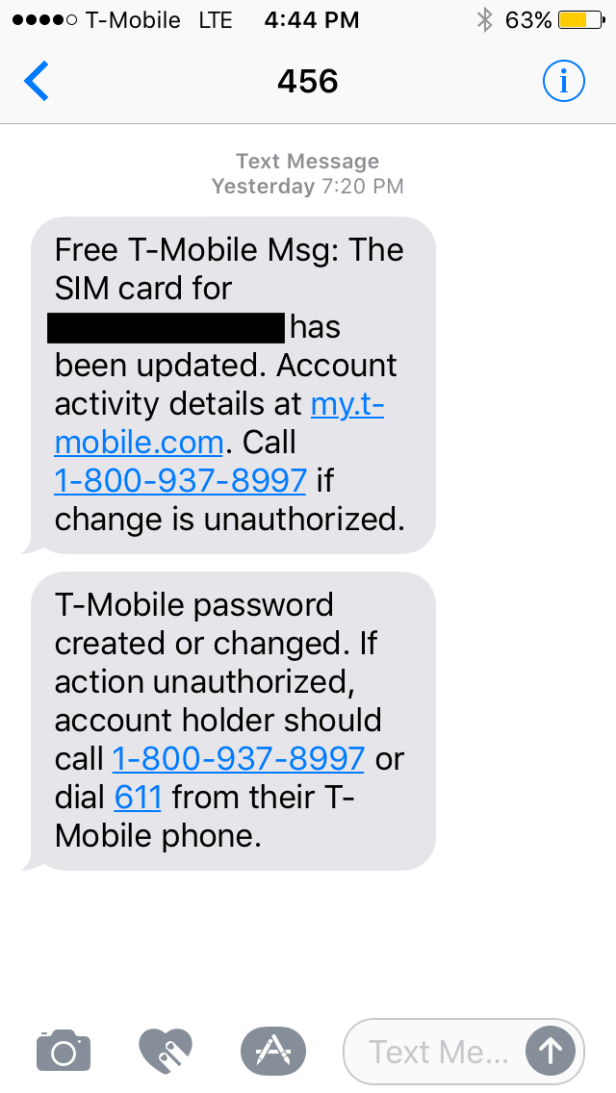
Huh. That’s odd. Then her phone stops working. Almost as if her SIM card was disabled, or something to that effect.
And considering what we both know about SMS-based 2FA and how many services rely on it, we both start getting worried. So my wife immediately gets on the phone with T-Mobile on my phone, and after maybe 20 minutes of navigating customer service reps, finally gets to someone who is able to see what is going on and shut this shit down.
The manager identifies that additional lines have been added to our account (um okay – it was at this point that my wife asked “What is this Wells Fargo shit that you’re pulling?”), and that my wife’s number has been changed to a different device (um what). This is undone, and our account is locked. Also we changed our account settings to only allow account modification in person, in store, with ID – thankfully there is a T-Mobile store nearby.
For future reference note that our first call was to our mobile provider, and that it took about 20 minutes to get the action reversed.
Okay. That was Sunday. We didn’t know quite what was going on – was someone trying to sell our numbers? Was it the result of some “Wells Fargo shit” with a CSR chasing a quarterly bonus? – but we knew that our numbers were back and our T-Mobile account was locked down, so we were good.
Monday – 7 a.m.
My wife checked her email and saw messages from our bank that the following things had been changed:
- Password
- Security Questions
- PIN
So, THAT’S BAD.
My account was fine, so I logged in to see that our two checking accounts had been wiped clean, with several large transactions at Walgreens and Meijer.
Wife gets on the phone with the bank – and you’d think when you called a bank and said “all of the money from my checking accounts is gone” they would immediately send you to the fraud department, but instead there was some customer service bouncing before we finally got to someone who could do something.
Thankfully, we have confidence in our bank and even before getting on the phone were fairly certain the money would be restored via insurance or trust in capitalism or something similarly magical.
And after two hours on the phone – locking down the account (not even sure what that means, actually), disabling features (mobile wallet, SMS 2FA), verifying what were fraudulent charges and what were legit – all that we could do was done, and the manager at the bank said our money should be back within one or two business days (this has since happened, yay banking system).
Monday/Tuesday/Wednesday
My wife and I spend more time on the phone with the bank and T-Mobile checking on our account. Since this started, my wife has spent 22 hours on the phone dealing with it.
After that
Our money is back. T-Mobile gave two months of free service. I have been too busy to go through the work of changing providers, but I should probably do that. 2FA changes have been made (as explained under “Lessons Learned”).
